A reverse proxy is a type of proxy server that sits between a client and a web server, acting as an intermediary between the two. Unlike a forward pro
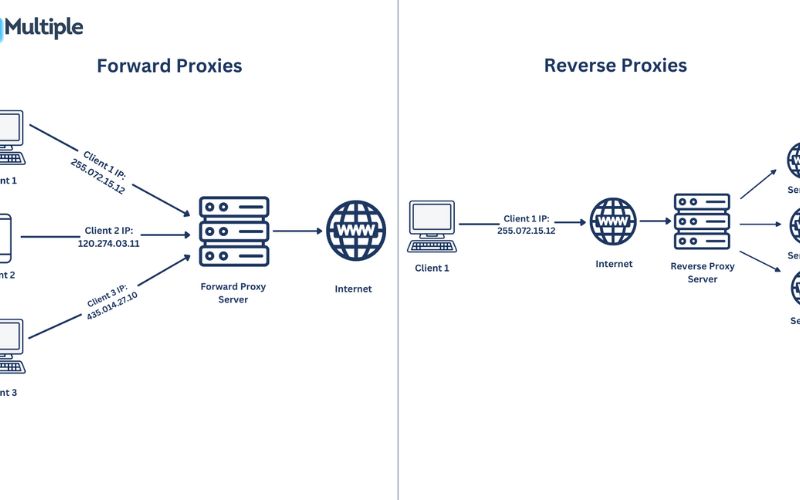
A reverse proxy is a type of proxy server that sits between a client and a web server, acting as an intermediary between the two. Unlike a forward proxy, which is used to hide a client’s identity and provide access to the internet, a reverse proxy is used to hide the identity of the web server and provide additional functionality, such as load balancing, caching, and security.
Reverse proxies are commonly used in web applications to improve performance, enhance security, and provide additional features that are not available on the web server itself. They act as a gateway, accepting incoming requests from clients and then forwarding those requests to the appropriate web server, before returning the response back to the client.
How Does Reverse Proxy Work?
The process of a reverse proxy working is as follows:
- The client sends a request to the reverse proxy, typically using the reverse proxy’s public IP address or domain name.
- The reverse proxy receives the request and analyzes it to determine the appropriate web server to forward the request to.
- The reverse proxy forwards the request to the selected web server, which processes the request and generates a response.
- The reverse proxy receives the response from the web server and then sends the response back to the client.
This process allows the reverse proxy to handle various tasks, such as load balancing, caching, and security, without the client or the web server being aware of the reverse proxy’s existence.
Benefits of Using a Reverse Proxy
Using a reverse proxy can provide several benefits, including:
- Load Balancing: Reverse proxies can distribute incoming traffic across multiple web servers, ensuring that no single server becomes overwhelmed and improving overall system performance.
- Caching: Reverse proxies can cache frequently accessed content, reducing the load on the web servers and improving response times for clients.
- Security: Reverse proxies can act as a protective layer, shielding web servers from direct client access and providing additional security measures, such as SSL/TLS termination, DDoS protection, and IP filtering.
- Scalability: Reverse proxies can be easily scaled up or down to handle changes in traffic volume, making it easier to manage and maintain web applications.
- Centralized Configuration: Reverse proxies allow you to manage and configure web server settings from a single, centralized location, simplifying the administration and maintenance of your web infrastructure.
Common Use Cases for Reverse Proxy
Reverse proxies are used in a variety of scenarios, including:
- Web Serving: Reverse proxies are commonly used to serve web content, handling tasks such as load balancing, caching, and SSL/TLS termination.
- API Management: Reverse proxies can be used to manage and secure access to APIs, providing features like authentication, rate limiting, and transformation.
- Content Delivery Networks (CDNs): Reverse proxies are a key component of CDNs, helping to distribute content from a central location to users around the world.
- Microservices Architecture: Reverse proxies can be used to manage and route traffic between different microservices, providing a unified entry point for clients.
- Legacy Application Integration: Reverse proxies can be used to integrate legacy applications with modern web infrastructure, providing a unified interface and additional functionality.
Types of Reverse Proxy Servers
There are several types of reverse proxy servers, each with its own set of features and capabilities:
- Web Server-based Reverse Proxies: These are reverse proxies that are built into web servers, such as Apache HTTP Server and Nginx.
- Standalone Reverse Proxies: These are dedicated reverse proxy applications, such as Squid, HAProxy, and Varnish, which can be installed and configured separately from the web server.
- Cloud-based Reverse Proxies: Many cloud providers, such as Amazon Web Services (AWS), Google Cloud, and Microsoft Azure, offer managed reverse proxy services that can be easily integrated into your web infrastructure.
The choice of reverse proxy server will depend on your specific requirements, such as the scale of your web application, the level of control you need, and the features you require.
Setting Up a Reverse Proxy
Setting up a reverse proxy typically involves the following steps:
- Choose a Reverse Proxy Server: Select the appropriate reverse proxy server based on your requirements, such as web server-based, standalone, or cloud-based.
- Configure the Reverse Proxy: Set up the reverse proxy by specifying the web servers it should forward requests to, as well as any additional configurations, such as load balancing, caching, and security settings.
- Integrate the Reverse Proxy: Integrate the reverse proxy into your web infrastructure, ensuring that it is properly configured to handle incoming traffic and forward requests to the appropriate web servers.
- Test and Optimize: Thoroughly test the reverse proxy setup to ensure it is working as expected, and make any necessary adjustments to optimize performance and security.
Best Practices for Configuring a Reverse Proxy
When configuring a reverse proxy, it’s important to follow best practices to ensure optimal performance and security. Some key best practices include:
- Secure the Reverse Proxy: Ensure that the reverse proxy is properly secured, with strong access controls, SSL/TLS encryption, and regular updates to address security vulnerabilities.
- Optimize Caching: Implement effective caching strategies to reduce the load on the web servers and improve response times for clients.
- Implement Load Balancing: Configure the reverse proxy to distribute incoming traffic across multiple web servers, ensuring that no single server becomes overwhelmed.
- Monitor and Troubleshoot: Regularly monitor the reverse proxy and the web servers it is managing, and be prepared to troubleshoot any issues that may arise.
- Automate and Scale: Automate the deployment and scaling of the reverse proxy to ensure that it can adapt to changes in traffic and infrastructure requirements.
Troubleshooting Common Issues with Reverse Proxy
While reverse proxies can provide numerous benefits, they can also introduce some challenges. Some common issues that may arise include:
- Connectivity Issues: Problems with the connection between the client and the reverse proxy, or between the reverse proxy and the web servers, can cause connectivity issues.
- Performance Bottlenecks: Poorly configured caching, load balancing, or other reverse proxy settings can lead to performance bottlenecks.
- Security Vulnerabilities: Improper configuration of the reverse proxy’s security settings can expose your web infrastructure to security risks.
- Compatibility Problems: Compatibility issues between the reverse proxy and the web servers or other components in your infrastructure can cause problems.
To troubleshoot these issues, it’s important to have a good understanding of the reverse proxy’s configuration, as well as the overall architecture of your web infrastructure. Monitoring and logging tools can be particularly helpful in identifying and resolving problems.
Security Considerations for Reverse Proxy
Reverse proxies can provide an additional layer of security for your web infrastructure, but they also introduce their own set of security considerations. Some key security considerations for reverse proxies include:
- SSL/TLS Termination: Ensure that the reverse proxy is properly configured to handle SSL/TLS termination, and that it is using the latest and most secure protocols.
- Access Control: Implement robust access control measures to prevent unauthorized access to the reverse proxy and the web servers it manages.
- DDoS Protection: Configure the reverse proxy to provide protection against distributed denial-of-service (DDoS) attacks, which can overwhelm the web infrastructure.
- Logging and Monitoring: Implement comprehensive logging and monitoring of the reverse proxy to detect and respond to security incidents.
- Regular Updates and Patches: Keep the reverse proxy and its underlying components up-to-date with the latest security patches and updates to address known vulnerabilities.
By addressing these security considerations, you can help ensure that your reverse proxy and the web infrastructure it supports are well-protected against a wide range of security threats.
Conclusion
Reverse proxies are a powerful tool for improving the performance, security, and scalability of web applications. By acting as an intermediary between clients and web servers, reverse proxies can provide a range of benefits, including load balancing, caching, and enhanced security.
Whether you’re running a small website or a large-scale web application, understanding the role of reverse proxies and how to configure them effectively can be a valuable asset in your web infrastructure toolkit. By following best practices and addressing security considerations, you can ensure that your reverse proxy is a reliable and secure component of your overall web architecture.
If you’re looking to improve the performance and security of your web application, consider implementing a reverse proxy. Our team of experts can help you choose the right reverse proxy solution and guide you through the setup and configuration process. Contact us today to learn more.
COMMENTS