A proxy server is a computer or network device that acts as a gateway between a user's device and the internet. When you access a website or online re
A proxy server is a computer or network device that acts as a gateway between a user’s device and the internet. When you access a website or online resource, your request first goes through the proxy server before reaching its final destination. This intermediary role allows the proxy server to perform various tasks, such as filtering content, caching data, and enhancing security.
Proxy servers have been around for decades, but their importance has grown significantly in recent years as the internet has become an integral part of our daily lives. Whether you’re an individual seeking to protect your online privacy or a business looking to enhance network security, understanding the role of proxy servers is crucial.
How Does a Proxy Server Work?
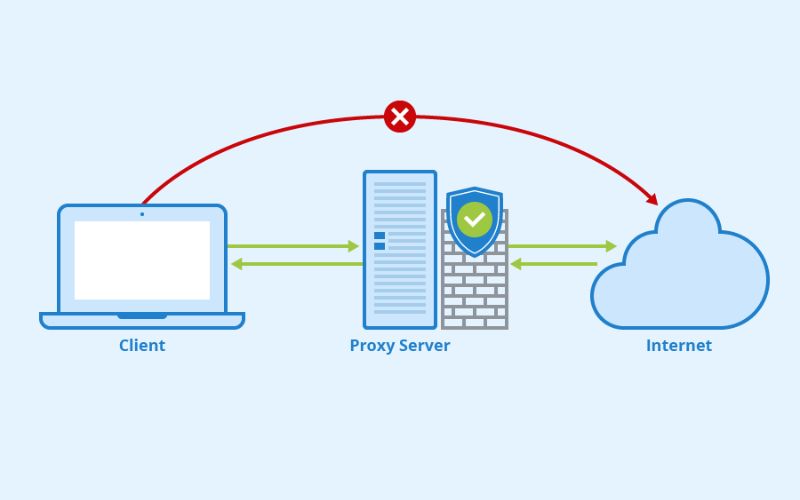
The process of using a proxy server is relatively straightforward. When you initiate an online request, your device sends the request to the proxy server instead of directly to the target website or resource. The proxy server then forwards the request to the intended destination and retrieves the response, which it then sends back to your device.
This indirect communication allows the proxy server to perform various functions, such as:
- IP Address Masking: The proxy server can hide your actual IP address, replacing it with its own, which can help protect your online privacy and prevent certain types of tracking or geo-restrictions.
- Content Filtering: Proxy servers can be configured to filter out specific types of content, such as inappropriate or malicious websites, before delivering the requested information to your device.
- Data Caching: Proxy servers can cache frequently accessed data, reducing the load on the original server and improving response times for users.
- Security Enhancement: Proxy servers can act as a barrier between your device and potential online threats, helping to prevent unauthorized access, malware, and other security risks.
Types of Proxy Servers
There are several different types of proxy servers, each with its own unique features and use cases. Some of the most common types include:
- Web Proxy: A web proxy is the most basic type of proxy server, designed to handle HTTP and HTTPS traffic. It can be used to bypass content filters, access blocked websites and hide your IP address.
- Transparent Proxy: A transparent proxy is a type of proxy server that does not require any special configuration on the client-side. It intercepts and forwards web traffic without the user’s knowledge or involvement.
- Anonymous Proxy: An anonymous proxy server hides your IP address and other identifying information, providing a higher level of online privacy and anonymity.
- Reverse Proxy: A reverse proxy is used on the server side to provide load balancing, caching, and security features for web applications and services.
- SOCKS Proxy: SOCKS proxies can handle a wider range of network protocols, including TCP and UDP, making them more versatile than web-based proxies.
- SSL/TLS Proxy: SSL/TLS proxies are designed to handle encrypted traffic, providing an additional layer of security for sensitive online activities.
Depending on your specific needs and the level of privacy or security you require, you may choose to use one or more of these proxy server types.
Benefits of Using a Proxy Server
Using a proxy server can provide a wide range of benefits, both for individuals and organizations. Some of the key advantages include:
- Enhanced Privacy: Proxy servers can mask your IP address and hide your online activities from prying eyes, helping to protect your personal information and online identity.
- Bypassing Restrictions: Proxy servers can help you access websites or online content that may be blocked or restricted in your location, allowing you to bypass censorship or geo-restrictions.
- Improved Performance: Proxy servers can cache frequently accessed data, reducing the load on the original servers and improving response times for users.
- Increased Security: Proxy servers can act as a barrier between your device and potential online threats, helping to prevent unauthorized access, malware, and other security risks.
- Centralized Management: For organizations, proxy servers can provide a centralized point of control for managing and monitoring internet access, improving security and compliance.
- Bandwidth Optimization: Proxy servers can compress data, optimize network traffic, and help manage bandwidth usage, particularly in environments with limited or metered internet connections.
Common Use Cases for Proxy Servers
Proxy servers have a wide range of applications, catering to the needs of both individuals and organizations. Some of the most common use cases include:
- Online Privacy and Anonymity: Individuals use proxy servers to protect their online privacy, hide their IP addresses, and bypass censorship or geo-restrictions.
- Content Filtering and Access Control: Organizations use proxy servers to filter out inappropriate or malicious content, while also controlling and monitoring employee internet usage.
- Network Security: Proxy servers can help organizations enhance their network security by acting as a barrier against cyber threats, such as malware and unauthorized access.
- Bandwidth Management: Proxy servers can be used to optimize network traffic and manage bandwidth usage, particularly in environments with limited or metered internet connections.
- Remote Access: Proxy servers can enable remote access to resources, allowing users to securely connect to internal networks or applications from outside the organization.
- Content Caching and Load Balancing: Proxy servers can cache frequently accessed data and distribute the load across multiple servers, improving website performance and reducing the strain on the original infrastructure.
Proxy Server Security Considerations
While proxy servers offer numerous benefits, it’s important to be aware of the potential security risks and considerations associated with their use. Some key factors to keep in mind include:
- Trust in the Proxy Provider: When using a third-party proxy service, it’s crucial to ensure that the provider is reputable and trustworthy, as they will have access to your internet traffic and potentially sensitive information.
- Encryption and Data Security: Ensure that the proxy server uses strong encryption protocols, such as SSL/TLS, to protect your data in transit and prevent eavesdropping or tampering.
- Logging and Monitoring: Understand the proxy server’s logging and monitoring practices, as some providers may keep records of your online activities, which could compromise your privacy.
- Malware and Vulnerabilities: Proxy servers, like any other software or network component, can be vulnerable to security threats, such as malware or exploits. Keep your proxy server software up-to-date and ensure that it is properly configured to mitigate these risks.
- Compliance and Regulations: Depending on your location and industry, there may be specific regulations or compliance requirements that you need to consider when using a proxy server, such as data protection laws or content filtering policies.
By addressing these security considerations and choosing a reputable proxy service, you can maximize the benefits of using a proxy server while minimizing the potential risks.
Choosing the Right Proxy Server for Your Needs
When selecting a proxy server, it’s important to consider your specific needs and requirements. Some key factors to keep in mind include:
- Purpose and Functionality: Determine the primary purpose for using a proxy server, such as privacy, security, content filtering, or performance optimization, and choose a solution that best fits your requirements.
- Supported Protocols: Ensure that the proxy server supports the necessary protocols, such as HTTP, HTTPS, SOCKS, or SSL/TLS, depending on your use case.
- Speed and Performance: Consider the proxy server’s performance, including response times, throughput, and the ability to handle high traffic loads, especially if you have a large number of users or need to access data-intensive resources.
- Logging and Monitoring: Evaluate the proxy server’s logging and monitoring capabilities, as well as its data retention policies, to ensure alignment with your privacy and compliance requirements.
- Security and Encryption: Prioritize proxy servers that offer robust security features, such as strong encryption, authentication, and protection against common cyber threats.
- Scalability and Flexibility: Depending on your needs, choose a proxy server solution that can scale up or down to accommodate changes in your user base or traffic patterns, and that provides the flexibility to customize settings and configurations.
- Pricing and Cost: Consider the overall cost of the proxy server solution, including any subscription fees, bandwidth usage charges, or additional features that may incur additional expenses.
By carefully evaluating these factors, you can select the proxy server that best meets your requirements and provides the optimal balance of functionality, security, and cost-effectiveness.
Setting Up and Configuring a Proxy Server
The process of setting up and configuring a proxy server can vary depending on the specific solution you choose and the requirements of your organization or individual use case. However, the general steps typically involve:
- Selecting a Proxy Server Solution: Choose a reputable proxy server provider or software that meets your needs, such as a commercial service, an open-source solution, or a self-hosted proxy server.
- Network Configuration: Integrate the proxy server into your network infrastructure, ensuring that it is accessible to the devices or users that need to utilize it.
- Proxy Server Configuration: Set up the proxy server’s settings, such as the listening port, authentication credentials, and any necessary content filtering or security rules.
- Client Configuration: Depending on the proxy server type, configure the client devices (e.g., web browsers, mobile apps, or network settings) to route their internet traffic through the proxy server.
- Monitoring and Maintenance: Regularly monitor the proxy server’s performance, security logs, and any updates or patches that may need to be applied to ensure its continued effectiveness and reliability.
The specific steps involved in setting up and configuring a proxy server can be complex, and it’s often recommended to consult with IT professionals or refer to the documentation provided by the proxy server solution you choose.
Proxy Server Alternatives
While proxy servers are a widely used solution for enhancing online privacy, security, and performance, there are also alternative technologies and approaches that can achieve similar goals. Some of the most prominent proxy server alternatives include:
- Virtual Private Networks (VPNs): VPNs create a secure, encrypted tunnel between your device and the internet, providing an additional layer of privacy and security.
- Tor Network: The Tor network is a decentralized, volunteer-run network that routes your internet traffic through multiple layers of encryption, offering a high degree of anonymity.
- DNS Proxy Servers: DNS proxy servers can be used to bypass content restrictions and enhance privacy by routing your DNS requests through a different server.
- Onion Routing: Onion routing, similar to the Tor network, uses multiple layers of encryption and random routing to protect user privacy and anonymity.
- Browser-Based Privacy Extensions: Browser extensions, such as privacy-focused add-ons or incognito/private browsing modes, can provide some level of online privacy and security.
While these alternatives may offer different features and functionalities, proxy servers remain a popular and widely-used solution for a variety of use cases. The choice between a proxy server and an alternative solution will depend on your specific needs, the level of privacy and security required, and the overall performance and reliability of the chosen option.
Conclusion
In the ever-evolving digital landscape, where online privacy, security, and performance are of paramount concern, the role of proxy servers has become increasingly crucial. By acting as an intermediary between your device and the internet, proxy servers can provide a wide range of benefits, from enhanced privacy and security to improved performance and content access.
As you navigate the digital world, understanding the fundamentals of proxy servers, their various types, and the considerations involved in choosing and configuring the right solution can empower you to make informed decisions and take control of your online experience.
Whether you’re an individual seeking to protect your online privacy or an organization looking to enhance your network security, explore the world of proxy servers and discover how they can transform your digital journey. Contact us today to learn more about our comprehensive proxy server solutions and how they can benefit your specific needs.
COMMENTS