In the digital age, where online privacy and security are paramount, the concept of a proxy has become increasingly important. A proxy, in simple term
In the digital age, where online privacy and security are paramount, the concept of a proxy has become increasingly important. A proxy, in simple terms, is an intermediary server that acts as a gateway between your device and the internet. It intercepts your online requests, processes them, and then forwards them to the intended destination, acting as a shield between you and the rest of the web.
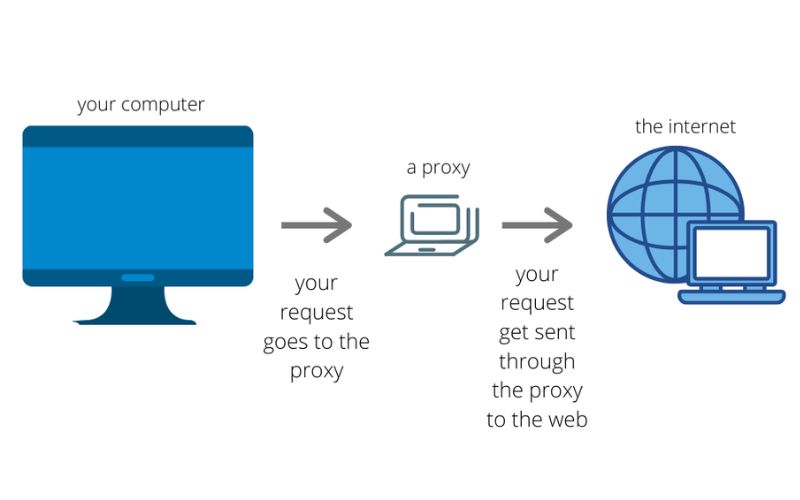
How Do Proxies Work?
When you use a proxy, your internet traffic is routed through the proxy server instead of directly connecting to the websites or services you’re trying to access. This process involves the following steps:
- Your device sends a request to the proxy server.
- The proxy server receives the request, processes it, and then forwards it to the intended destination on the internet.
- The response from the destination is sent back to the proxy server.
- The proxy server then sends the response back to your device.
This intermediary step allows the proxy server to perform various functions, such as filtering, caching, and even modifying the content before it reaches your device.
Types of Proxies
Proxies come in different forms, each with its own set of features and use cases. Some of the most common types of proxies include:
- Web Proxies: These proxies are primarily used to access websites and web-based applications, often bypassing content restrictions or censorship.
- Transparent Proxies: These proxies are used by organizations to monitor and control the internet usage of their employees or network users.
- Anonymous Proxies: These proxies hide your IP address and identity, providing a higher level of privacy and anonymity.
- Reverse Proxies: These proxies are used by web servers to handle incoming requests, offloading tasks such as SSL/TLS termination and load balancing.
- HTTP Proxies: These proxies handle HTTP and HTTPS traffic, allowing for more control and monitoring over web-based activities.
- SOCKS Proxies: These proxies can handle a wider range of protocols, including TCP and UDP, making them more versatile than HTTP proxies.
Benefits of Using a Proxy
Using a proxy offers a range of benefits, including:
- Privacy and Security: Proxies can help protect your online privacy by hiding your IP address and encrypting your internet traffic, making it more difficult for third parties to track your online activities.
- Bypass Restrictions: Proxies can be used to access websites or content that may be blocked or restricted in your location, such as social media platforms or streaming services.
- Improved Performance: Proxies can cache frequently accessed content, reducing the time it takes to load websites and improving overall browsing speed.
- Anonymity: Proxies can provide a higher level of anonymity by masking your real IP address and making it more difficult for websites to track your online activities.
- Parental Controls: Proxies can be used to filter and restrict access to certain websites or online content, making them a useful tool for parents to monitor and control their children’s internet usage.
Common Uses of Proxies
Proxies have a wide range of applications, including:
- Access Restricted Content: Proxies are often used to bypass content restrictions and access websites or online services that may be blocked in certain regions or by certain organizations.
- Online Privacy and Security: Proxies can help protect your online privacy by hiding your IP address and encrypting your internet traffic, making it more difficult for third parties to track your activities.
- Bypass Censorship: Proxies can be used to circumvent censorship and access information that may be restricted or blocked by governments or other entities.
- Improve Network Performance: Proxies can cache frequently accessed content, reducing the load on your network and improving overall browsing speed.
- Parental Controls: Proxies can be used to filter and restrict access to certain websites or online content, making them a useful tool for parents to monitor and control their children’s internet usage.
Proxy Server Setup and Configuration
Setting up a proxy server can be a straightforward process, but the specific steps may vary depending on the type of proxy and the device or operating system you’re using. Generally, the process involves the following steps:
- Choose a Proxy Provider: Select a reputable proxy service that meets your needs in terms of features, performance, and security.
- Configure Your Proxy Settings: Depending on your device and operating system, you’ll need to update your network settings to route your internet traffic through the proxy server.
- Test Your Proxy Connection: Verify that your proxy is working correctly by visiting a website or service that can check your IP address and location.
It’s important to note that the configuration process may differ across various devices and operating systems, so it’s always a good idea to refer to the specific instructions provided by your proxy provider or the documentation for your device.
Proxy Security and Privacy Concerns
While proxies can offer a range of benefits, it’s important to be aware of the potential security and privacy concerns associated with their use:
- Trust in the Proxy Provider: When using a proxy, you’re entrusting your internet traffic and potentially sensitive information to the proxy provider, so it’s crucial to choose a reputable and trustworthy service.
- Potential for Logging and Monitoring: Some proxy providers may log or monitor your internet activity, which could compromise your privacy and security.
- Vulnerability to Attacks: Proxy servers can be vulnerable to various types of attacks, such as man-in-the-middle attacks, which could compromise your data and online security.
- Potential for Malware Injection: Untrustworthy proxy providers may inject malware or other malicious code into your internet traffic, putting your device and personal information at risk.
To mitigate these concerns, it’s essential to research and select a proxy provider with a strong reputation for security and privacy, and to regularly monitor and update your proxy settings to ensure optimal protection.
Choosing the Right Proxy Provider
When selecting a proxy provider, there are several factors to consider to ensure you choose the right one for your needs:
- Security and Privacy: Look for a provider that offers strong encryption, a strict no-logs policy, and a commitment to protecting your online privacy.
- Performance: Consider the provider’s server locations, connection speeds, and overall network performance to ensure a smooth and reliable browsing experience.
- Compatibility: Make sure the proxy provider offers support for the devices and operating systems you use, as well as the specific protocols and applications you need to access.
- Pricing and Plans: Evaluate the provider’s pricing structure and subscription plans to find one that fits your budget and usage requirements.
- Reputation and Reviews: Research the provider’s reputation in the industry, read customer reviews, and look for any third-party certifications or audits that validate their claims.
By carefully evaluating these factors, you can find a proxy provider that best meets your needs and provides a secure and reliable online experience.
Proxy Troubleshooting and Common Issues
While proxies can be a valuable tool, you may encounter various issues during setup or usage. Some common problems and their potential solutions include:
- Connectivity Issues: If you’re unable to connect to the proxy server, check your network settings, firewall configurations, and the status of the proxy service.
- Slow Performance: Slow connection speeds may be due to server load, network congestion, or a mismatch between your location and the proxy server’s location. Try switching to a different server or adjusting your proxy settings.
- Blocked Websites: If certain websites or online services are still inaccessible, the proxy may not be able to bypass the specific restrictions or censorship in place.
- IP Leaks: If your real IP address is still being exposed, check for DNS leaks or other potential vulnerabilities in your proxy configuration.
- Compatibility Problems: Ensure that your device and applications are compatible with the proxy protocol and settings you’re using.
If you encounter any persistent issues, it’s recommended to reach out to your proxy provider’s customer support for further assistance and troubleshooting.
Conclusion
In the ever-evolving digital landscape, where online privacy and security are increasingly crucial, the role of proxies has become more essential than ever. By acting as an intermediary between your device and the internet, proxies can help protect your personal information, bypass content restrictions, and improve your overall online experience.
As you navigate the digital world, it’s important to understand the various types of proxies, their benefits, and their potential drawbacks. By choosing a reliable and trustworthy proxy provider, you can enjoy the advantages of enhanced privacy, security, and accessibility, all while mitigating the risks associated with proxy usage.
If you’re ready to take control of your online privacy and security, consider exploring the benefits of using a proxy. Visit our website to learn more about our trusted proxy services and how they can help you navigate the digital landscape with confidence.
COMMENTS